Investigating Urban Civil Power Infrastructure Resilience Using Cyber-Physical Co-Simulation Environments
Written by Ömer Sen, Dennis van der Velde, and Philipp Linnartz
With the increasing digitization of smart grids, especially urban civil power infrastructures, new opportunities for grid operation but also potential threats emerge that endanger the power supply. In order to investigate the cyber-physical resilience of new use cases, a co-simulation environment is developed that allows a detailed simulation of multiple domains of interest. In particular, flexibility coordination of distributed energy resources in combination with threat analysis of cyberattacks provides the first foundations for a holistic investigation environment for cyber-physical resilience.
Statement of the Challenge
In Smart Grids (SGs), in particular Urban Civil Power Infrastructures (UCPI), digitization is leading to increasing integration of Information and Communication Technology (ICT). This provides enhanced grid observability using real-time monitoring of the grid. It also offers opportunities for active control of individual assets of the system. This opens up new potential in the area of active operational management at the distribution grid level. In particular, flexibility resources provided by new types of (distributed) generation and consumers at the UCPI level can be used in an optimizing manner, both market- and grid-orientated. Multi-use concepts developed for this purpose are the subject of current research [1]. In addition to the acquisition of new potentials, the increasing inclusion of ICT in grid-relevant operations also requires the fulfilment of fundamental requirements for cyber-resilience and cybersecurity of the overall system [2]. Malfunctions in the ICT domain can have a direct impact on the security of supply [3]. In particular, adequate measures are needed to prevent cyberattacks to counter the increased attack surface. This requires providing communications data from attack patterns that can be used to develop, validate, and test such measures [4]. However, such data is not publicly available [5]. Both the development of new operational management concepts and the investigation of domain-specific cybersecurity measures require tailored development environments that share essential requirements in terms of their scalability, realism (e.g., digital twin), and flexibility [6].
Technological Innovation
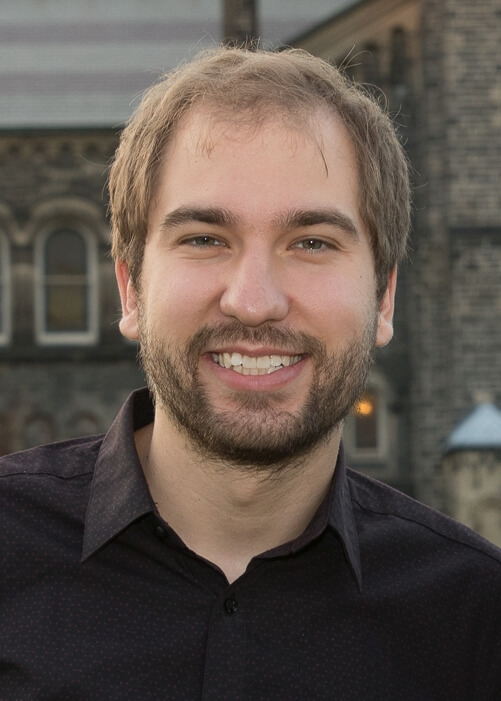
There are already various approaches in current research that depict SGs both using hardware within laboratories and software in the sense of a simulation. For instance, software-in-the-Loop co-simulation is used for the preliminary testing of SG software rollouts [7], while other approaches are used to simulate cyberattacks in SGs [8]. As part of the developments, a common environment is required in which models connecting both hardware and software components are implemented for interoperability (cf. Figure 1). This is particularly important when studying the resilience of SGs concerning interdependencies with ICT and emerging cyber threats. Despite a variety of preventive measures such as strict user management, password policies, access control, and network segmentation, intrusion detection capabilities are still needed to meet the high-security requirements in SGs. A holistic security concept, consisting not only of preventive measures but also of detective and reactive measures, can provide options for counteracting successful intruders. Several approaches address the analysis of cybersecurity by investigating cyberattack scenarios, e.g., denial-of-service attacks, false data injection, or a physical system disruption technique, using mathematical modelling or cyberattack trees [9]. In addition, several co-simulation approaches are being explored that consider hardware-in-the-loop co-simulation or a synthetic framework to simulate attack scenarios in SG applications to generate normal and attack data [10]. Co-simulation can thus leverage isolated and real-time simulation methods to perform a variety of services and vulnerabilities that allow simulating a dynamic, multi-stage attacker exploring the network and exploiting found vulnerabilities in a virtual, as well as a cyber-physical, environment [11].
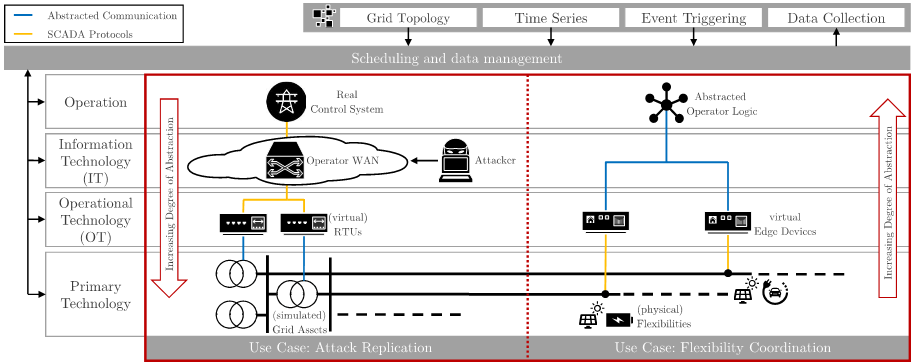
Figure 1: Illustration of a co-simulation environment representing a multiple use-case scenario
Importance and Potential
With the increasing interconnection between power systems and ICT, understanding and studying the interdependencies concerning cyber-physical systems becomes critical for the sustainable integration and operation of smart grids. Applications relevant to the sustainable implementation of a smart grid are not only the study of the performance of the simulated domains under the respective constraints stemming from their counter-domain, it also encompasses the study of the impact of certain threats that arise and need to be studied as a consequence of this increasing convergence between operational and information technologies. For example, investigating threats from cyberattacks, misconfigured, failed, or performance-constrained ICT components that have a negative technical impact on the cyber-physical system and grid operations are topics that can be investigated through co-simulation (cf. Figure 2). The co-simulation environments also enable explainable and reproducible test procedures or benchmark tests can be carried out. This can be used for the validation of developed tools and approaches. This concerns not only software-based components, but also hardware-in-the-loop simulations or derivations of such simulation approaches. The requirements for the co-simulation environment depend on the use case to be realized and mainly concern the scalability of the simulation capabilities, the level of detail of the models/simulations, and the interoperability with hardware, software, and other simulations. Simulation of large-scale cyber-physical systems with high fidelity and interoperability is thus a major challenge in its realization but offers significant value for studying the current and future development of cyber-physical systems in terms of reliability, resilience, security, and stability.
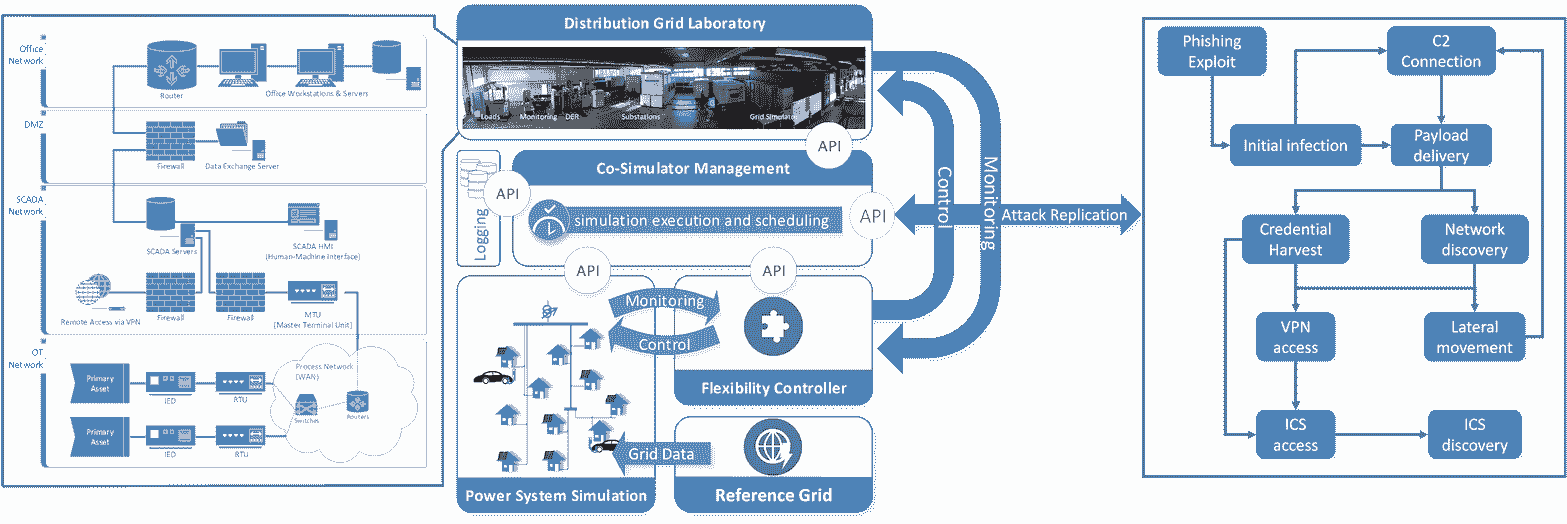
Figure 2: Illustration of the co-simulation environment in the laboratory environment.
Deployment Methodology
Co-simulation uses an integration tool to connect (and synchronize) multiple simulations that are not inherently on the same simulation platform or compatible (cf. Figure 3). Simulations are run on the respective simulation platforms and coordination is handled by one element. Data is passed through an interface to transmit power system data to the cyber simulation and vice versa. Co-simulation can thus be deployed on one (virtual) machine or distributed across several, which also enables cloud-based deployments. In terms of interaction with real hardware and components - e.g., real network devices, real communication networks, grid control devices, or grid protection devices - synchronization between the cyber simulation and the physical simulation is required, which must also be done in real-time. This is necessary for the real hardware to receive realistic stimuli as in a real system, which requires interoperable interfaces to the real hardware.
Figure 3: Illustration of the cyber-physical use of co-simulation
Anticipated Risks and Mitigation Strategies
Depending on the use case, different requirements are made and therefore different techniques have to be sought within the simulation. In particular, co-simulation of domains within power grids perceived as cyber-physical systems can be broken down into the following requirements:
- Mapping system behavior must encapsulate physical action and intelligent control that processes information and communicates with other components
- Addressing synchronization bottlenecks in the simulation of complex large power systems involving the cyber-physical layers in terms of scalability
- Efficient data management for large-scale co-simulation to reduce the potential negative technical impact on performance or quality of output data
- Interoperability with other simulation environments, but also providing interfaces for interaction with physical components
The above requirements define the approach of co-simulation in terms of mapping the behavior and interaction in the system. For example, the use case of analyzing the impact of certain operational management concepts on the grid under specific cyber conditions does not necessarily require a fully detailed simulation method. In particular, if only the interaction of cyber and physical systems in a steady-state perspective is of interest, a discrete and event-based representation of the system behavior may be sufficient to represent the required system detail. However, other use cases require a different level of simulation detail, which, in itself, has an inclusive nature, i.e., use cases with lower detail requirements can also be represented with co-simulation tailored to use cases with higher levels of detail.
Benefits and Impacts
Through the holistic approach of co-simulation of SG with different use cases, the study of complex cyber-physical systems can be performed under specific conditions to analyze the performance and also potential threats. With the increasing digitization in power systems, where operational and information technologies converge, it is necessary to study cross-domain interactions and cascading influences to ensure a reliable, secure, stable, and resilient infrastructure. This extends not only to the perspective of critical infrastructure components, systems, and architectures; but also to use cases in terms of services, logic, and operational management concepts. Therefore, a flexible and scalable approach in simulating different aspects of SG is essential for sustainable integration of current, but future-oriented SG use cases.
Conclusions
Co-simulation environments can be used to study domain-specific use cases such as cybersecurity and SG operational concepts. Co-simulation allows the abstraction level of all components to be adjusted depending on the use cases. For example, co-simulation enables the study of flexibility coordination, performance analysis of specific systems, resilience with respect to independent technologies, and threats such as cyberattacks. In terms of attack replication, reference scenarios or benchmark datasets can be generated to develop countermeasures such as intrusion detection. Combined with the integration of operational management concepts to control decentralized flexibilities in the environment, complex use cases can be examined under specific threat conditions. This thus forms the basis for further developments in the area of multi-use strategies and cyber resilience of such networked systems.
References
- Cong Nam and Schimpe, Michael and B, 2018, "Multi-use of stationary battery storage systems with blockchain based markets", Energy Procedia, Elsevier, 3--16.
- Dennis and Henze, Martin and Kathmann, Philipp and Wassermann, Erik and Andres, Michael and Bracht, Detert and Ernst, Raphael and Hallak, George and Klaer, Benedikt and Linnartz, Philipp and others van der Velde, 2020, "Methods for Actors in the Electric Power System to Prevent, Detect and React to ICT Attacks and Failures", 2020 6th IEEE International Energy Conference (ENERGYCon), IEEE, 17--22.
- Benedikt and Sen, Ömer and van der Velde, Dennis and Hacker, Immanuel and Andres, Michael and Henze, Martin Klaer, 2020, "Graph-based Model of Smart Grid Architectures", 2020 International Conference on Smart Energy Systems and Technologies (SEST), IEEE, 1--6.
- Ömer and van der Velde, Dennis and Wehrmeister, Katharina A and Hacker, Immanuel and Henze, Martin and Andres, Michael Sen, 2021, "Towards an Approach to Contextual Detection of Multi-Stage Cyber Attacks in Smart Grids", 2021 International Conference on Smart Energy Systems and Technologies (SEST), IEEE, 1--6.
- Richard and Khoshgoftaar, Taghi M and Wald, Randall Zuech, 2015, "Intrusion detection and big heterogeneous data: a survey", Journal of Big Data, Springer, 1--41.
- Dennis and Sen, Ömer and Hacker, Immanuel van der Velde, 2021, "Towards a Scalable and Flexible Smart Grid Co-Simulation Environment to Investigate Communication Infrastructures for Resilient Distribution Grid Operation", 2021 International Conference on Smart Energy Systems and Technologies (SEST), IEEE, 1--6.
- Large-Scale Co-Simulation of Power Grid and Communication Network Models with Software in the Loop, 2020, "GLarge-Scale Co-Simulation of Power Grid and Communication Network Models with Software in the Loop", arXiv preprint arXiv:2005.11369.
- Alexandre Gustavo and Bortolozzo, Marcelo Cardoso and da Silva, Eduardo Germano and Schaeffer-Filho, Alberto and Gaspary, Luciano Paschoal and Barcellos, Marinho Wermann, 2016, "ASTORIA: A framework for attack simulation and evaluation in smart grids", NOMS 2016-2016 IEEE/IFIP Network Operations and Management Symposium, IEEE, 273--280.
- Gregory and Viswanathan, Arun and Caldera, Carlos and Shrobe, Howard Falco, 2018, "A master attack methodology for an AI-based automated attack planner for smart cities", IEEE Access, IEEE, 48360--48373.
- Abdullah and Moussa, Bassam and Debbabi, Mourad and Youssef, Amr and Agba, Basile L and Kassouf, Marthe Albarakati, 2018, "Openstack-based evaluation framework for smart grid cyber security", 2018 IEEE International Conference on Communications, Control, and Computing Technologies for Smart Grids (SmartGridComm), IEEE, 1--6.
- Ömer and van der Velde, Dennis and Peters, Sebastian N and Henze, Martin Sen, 2021, "An Approach of Replicating Multi-Staged Cyber-Attacks and Countermeasures in a Smart Grid Co-Simulation Environment", CIRED21, IET.
This article was edited by Wentao Zhu
To view all articles in this issue, please go to August 2022 eNewsletter. For a downloadable copy, please visit the IEEE Smart Cities Resource Center.



To have the eNewsletter delivered monthly to your inbox, join the IEEE Smart Cities Community.
Past Issues
To view archived articles, and issues, which deliver rich insight into the forces shaping the future of the smart cities. Older eNewsletter can be found here. To download full issues, visit the publications section of the IEEE Smart Cities Resource Center.